HackTheBox Certified Web Exploitation Expert (CWEE) - massive goshs update
I recently passed the certification exam on HackTheBox Certified Web Exploitation Expert (CWEE), which was a challenging but fun course.
What an achievement c1sc0! 🎉
You are a certified hacker!
You have successfully passed the examination process for HTB Certified Web Exploitation Expert.
We know that was not an easy way towards reaching your goal. However, let your success make some noise! You deserve it.
The Exam
The exam itself is a black box and white box penetration testing engagement against a set of web applications. Once you click “Enter Exam” and accept the terms, you receive a letter of engagement outlining all objectives and scope, plus a report template to work from.
You have 10 days to work through the lab and submit a commercial-grade report. The lab is a dedicated instance — no other candidates interfere, and you can reset it at any time. Along the way you submit flags to track progress, but flags alone are not enough: you need to hit a minimum point threshold and have your report meet a specific quality bar to pass.
Results come back within 20 business days, though in my case I got words from them two days after submitting the report. If you don’t pass the first attempt, you get an instructor’s feedback and one free retake — but you have to start it within 14 days of receiving that feedback, otherwise the voucher expires. One thing worth mentioning: the certification has no expiration date.
Not only was the exam challenging, but it was good fun. The course, compared to OSWE, which I did back in 2022, was a bit more structured. At least it felt to me like a bit more straightforward. The modules in the lab were well structured and easy to follow. Working with either the PwnBox or the provided OpenVPN file was easy enough. It felt natural, as always. If you ever hacked on HackTheBox you had used it this way already.
One tip: use the provided PwnBox over OpenVPN for XSS, CSRF and SSRF scenarios. I had reliability issues with callbacks through OpenVPN, so sticking to the PwnBox will save you some headache.
I’d recommend everyone that is thinking about either getting CWEE or OSWE certified to start with CWEE and then do OSWE afterwards. But this is just my take on it, that I hold both certificates.

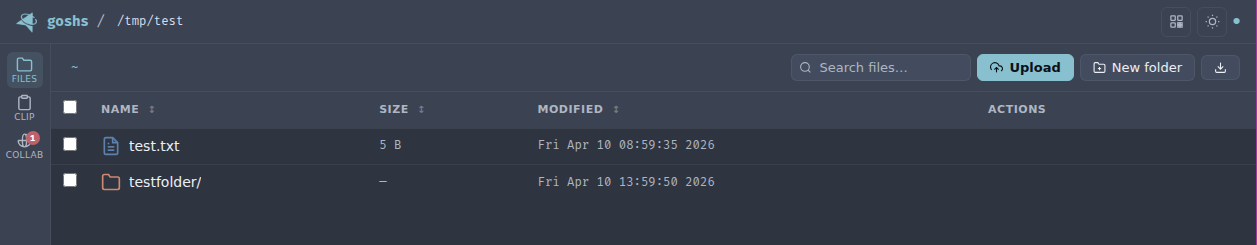
goshs v2.0.0 - A new goshs release
While working on the CWEE lab I had some cases of where I needed a victim to make a connection back to me. Often time Out-of-bound exfiltration was part of the exploit chain. The course provided useful snippets of python based web servers, that would handle these connections. While those are sufficient to pass the exam, I already had developed goshs some time ago and have ever since added features when I needed them. For example while doing all the OSCE³ certificates, some features were added. So it only felt natural to add features as I needed them while doing CWEE.
With the newest release of goshs, here’s what’s new:
- DNS Collaboration endpoint
- SMTP Collaboration endpoint
- SMB Server with Collaboration endpoint and hash extraction and cracking
?redirectendpoint to redirect victims to arbitrary locations- SMB server with NTLM hash capturing and cracking (not related to CWEE)
Not to spoil anything, but aside from the smb server feature, the others came in quite handy while doing the course and the exam.
Also I vastly polished up the UI to make goshs look more modern and to provide a better user experience.
Building the SMB Server in Go
The DNS and SMTP collaboration endpoints were relatively straightforward to implement. SMB was a different story entirely.
I built the SMB server from scratch in Go — no existing SMB library, just the protocol spec, Claude Code, and a lot of Wireshark captures.
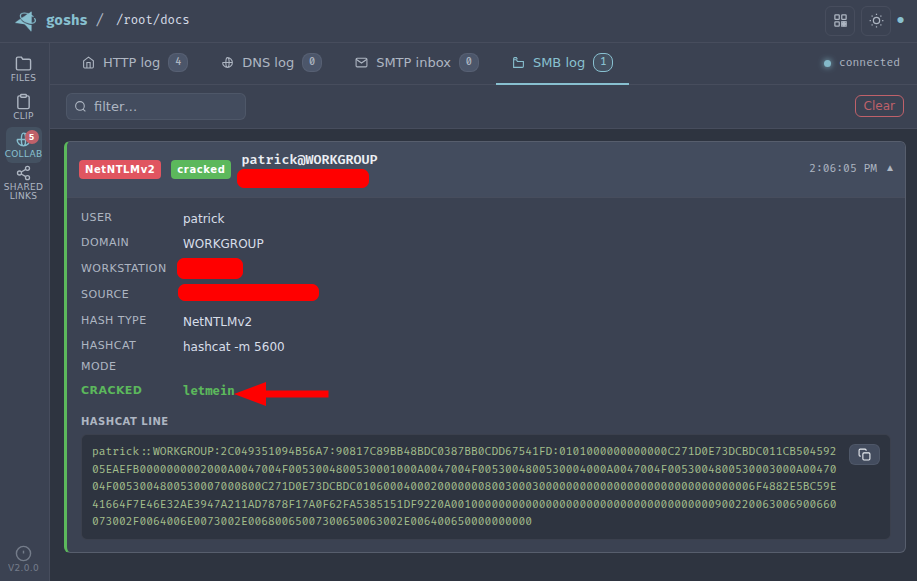
The NTLM hash capture part actually came together quickly. The handshake flow is well documented:
- A victim machine connects to the goshs SMB server
- goshs responds to the SMB negotiation, advertising NTLM authentication
- The victim sends an NTLM Type 1 (Negotiate) message
- goshs responds with a Type 2 (Challenge) message containing a crafted challenge
- The victim responds with a Type 3 (Authenticate) message containing the NTLMv2 hash
- goshs captures the hash in NetNTLMv2 format and attempts to crack it on the fly
The captured hash is in the same format as Responder output — it can be fed directly into hashcat or john if goshs doesn’t crack it on the fly.
Getting Linux clients working (smbclient, impacket’s smbclient.py, Nautilus) took a few days. Getting Windows 10 and 11 to connect natively took weeks. It was a long back and forth of implementing, testing, capturing traffic, and debugging.
The thing that accelerated development dramatically: exporting Wireshark captures as JSON and feeding them directly to Claude Code. Instead of describing protocol bugs in words, I could show exactly what was happening at the packet level. If you’re implementing any binary protocol in Go, this workflow is worth knowing about.
Windows 10 and 11 connect natively without any additional software on the victim side — just point them at your goshs instance via UNC path and the hash capture happens transparently.
I’ve only tested this against local (non-domain-joined) machines so far. If you’re in an enterprise environment with domain-joined hosts, I’d love to hear whether it works.
If you play CTFs on a regular basis or hack at HackTheBox, then you might wanna check out goshs at https://goshs.de for sure. Be sure to leave a ⭐ on GitHub, if you like it.
That’s it for now,
have a good one and cheers,
Patrick